
Uncompromising
Security
Delivers the highest-caliber threat prevention with award winning SandBlast Network Zero Day protection out of the box

Security at
Hyperscale
On-demand hyperscale threat prevention performance providing enterprises cloud level expansion and resiliency on premises

Unified Security
R80.40 unified security management control across networks, clouds, and IoT increases efficiency cutting security operations up to 80%
Introducing
NEW QUANTUM SECURITY GATEWAYS
All Quantum Security GatewaysTM come with Check Point’s award-winning
SandBlast Network right out of the box.
Check Point protects enterprises from the 5th Generation of sophisticated multi-vector cyber attacks
versus 3rd Generation of protection provided by other firewalls.

Quantum Security Gateways
- Best Security meets Ultimate Hardware
- SandBlast Network out of the box
- Modular hardware
- High Performance CPUs
- Expansion Slot Customization
- 100% Solid State Drives (SSD)
- and more…
Explore Next Generation Firewalls
Integrating the most advanced threat prevention and a consolidated management, our security gateway appliances are designed to prevent any cyber attack, reduce complexity and lower your costs.

Small Business
The most comprehensive, enterprise grade security for your business with intuitive and simple management & reporting using WebUIQuantum Spark, Provides the most comprehensive, enterprise grade security for your small and medium business with intuitive and simple management & reporting using WebUI

Industrial Appliances
Delivering Top-rated threat Prevention Ruggedized to protect the industrial. Control Systems for manufacturing, energy, utilities, and transportation.

Branch Office
Quantum Security Gateways provide enterprise-grade security in a small form factor, ideal for branch and small office

Midsize Enterprise
Quantum Security Gateways include the power of Gen V in a single security gateway engineered to meet all your business needs today and in the future

Large Enterprise
Quantum Security Gateways provide comprehensive security protections in a scalable, easy to manage configuration, preferred for large enterprises

Data Center and High-End Enterprise
The most comprehensive protections with data center-grade hardware to maximize uptime and performance

High Performance and Scalable Platforms
Multi-bladed, chassis-based security systems scale up to 66,000 SPU to support the needs of growing network
Remote Access VPN
Quantum VPN provides businesses of all sizes the ability to ensure best-in-class connectivity and security, allowing your workforce to remain as productive as possible
Event Management
SmartEvent, threat management is fully integrated, with login, monitoring, event correlation and reporting in one place.
Our Next Generation Firewall Prevent
Fifth-Gen of Cyber Attacks
Our Next Generation Firewalls focus on blocking malware and application-layer attacks. With more than 60 security services powered by the ThreatCloud, the world’s most powerful shared intelligence cloud service, our Quantum security gateways are able to react quickly and seamlessly to prevent known and unknown cyber attacks across the whole network. Our gateways enforce policies to better defend your network and carry out quick assessments to prevent invasive or suspicious activity, like unknown malware, and shut it down.

Highest Levels of Security with
Autonomous Threat Prevention
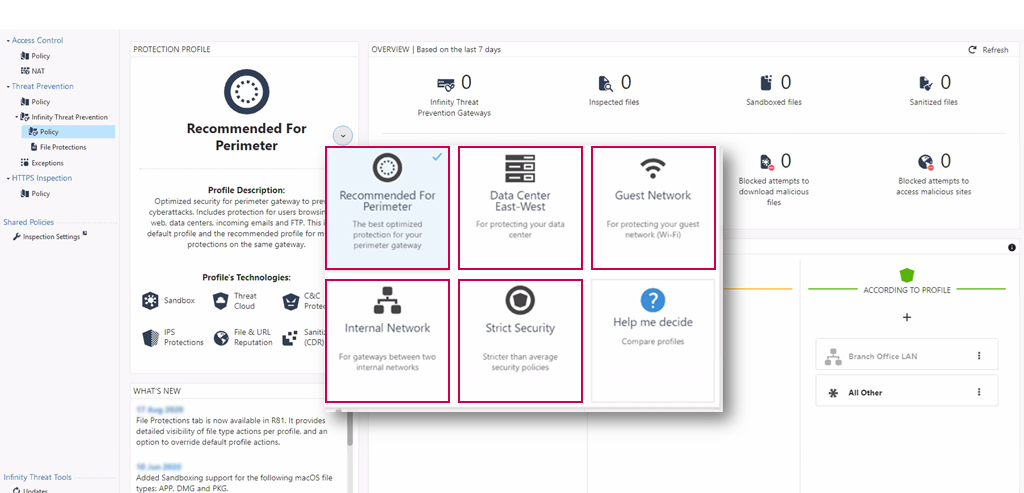

Absolute Zero Trust Security with Check Point Infinit
Zero Trust security is about having the ability to “Divide and Rule” your network in order to reduce the risk of lateral movement.
Check Point Next Generation Firewalls enable you to create granular network segmentation across public/private cloud and LAN environments. With detailed visibility into the users, groups, applications, machines and connection types on your network, they allow you to set and enforce a “Least Privileged” access policy. So, only the right users and devices can access your protected assets.





